Setting Up the Chipsailing CS9711 Fingerprint Reader on Linux Mint
If you’ve purchased a budget USB fingerprint reader (like the Chipsailing CS9711, USB ID 2541:0236) and found it undetected on Linux Mint, you aren’t alone. These “Match-on-Host” devices aren’t supported by default in libfprint, but they can be brought to life with a community driver.
Identifying the Hardware
First, verify your device ID by running lsusb in the terminal. Look for:
Bus XXX Device XXX: ID 2541:0236 Chipsailing CS9711Fingprint
If the device is detected but fails to “enumerate” (doesn’t show a name), ensure it is plugged directly into a motherboard USB port rather than a hub to provide consistent power.
Installation Steps
To get the reader working, you must build a patched version of libfprint that includes the CS9711 driver.
Install Dependencies
Open your terminal and install the required build tools and libraries:
sudo apt update && sudo apt install -y git build-essential meson ninja-build
libnss3-dev libgudev-1.0-dev libgusb-dev libpixman-1-dev libssl-dev
libopencv-dev doctest-dev fprintd libpam-fprintdBuild and Install the Driver
Clone the community repository and compile the source:
git clone https://github.com/archeYR/libfprint-CS9711.git
cd libfprint-CS9711
meson setup build
ninja -C build
sudo ninja -C build install
sudo ldconfig
sudo systemctl restart fprintdEnrollment and Verification
Once installed, you can manage your fingerprints directly from the command line.
- Enroll a finger: Run
fprintd-enroll. Be prepared to touch the sensor ~15 times. - Select a specific finger: Use the
-fflag, e.g.,fprintd-enroll -f right-thumb. - Test verification: Run
fprintd-verifyand scan your finger to confirm a match.
After verifying in the terminal, you can enable “Fingerprint Login” under System Settings > Users or run sudo pam-auth-update to enable it for sudo prompts.
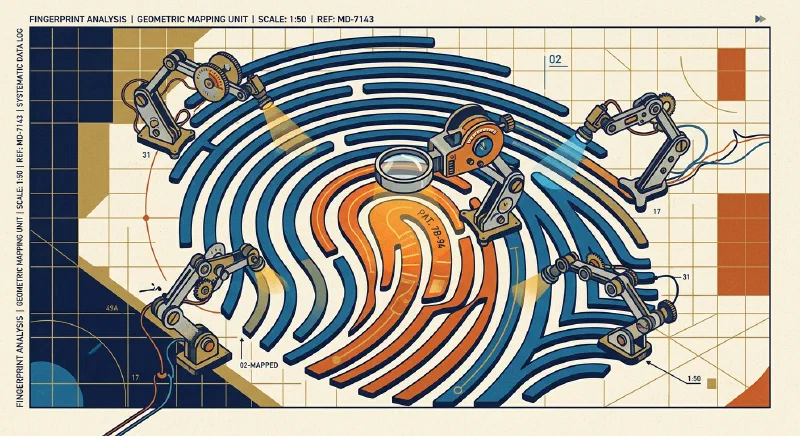
How It Works (Technical Overview)
Unlike high-end “Match-on-Chip” sensors, the CS9711 is a Match-on-Host device. This means all the intelligence lives in software on your PC rather than in dedicated silicon on the sensor itself. Here’s the full pipeline from touch to authentication:
Image Capture (USB HID)
When you press your finger on the sensor, the CS9711 captures a small grayscale bitmap—typically around 80×80 pixels at roughly 500 DPI. This raw image is streamed over the USB HID (Human Interface Device) protocol to the host system. Unlike more advanced sensors, the CS9711 performs no on-device processing or encryption; the pixel data is transmitted in plaintext.
The libfprint driver communicates with the device using a vendor-specific HID report format, handling the USB control transfers needed to trigger a scan and read back the image frame.
Image Enhancement (OpenCV)
Raw fingerprint images from budget sensors are often noisy, low-contrast, and subject to smearing. The driver passes the raw bitmap through an OpenCV image processing pipeline that applies:
- Histogram equalization to normalize contrast across the image
- Gaussian blur and unsharp masking to reduce noise while sharpening ridge detail
- Binarization (converting the gray image to black-and-white ridges) using adaptive thresholding
The goal is to produce a clean ridge map reliable enough for feature extraction.
Minutiae Extraction (NBIS / MINDTCT)
Once enhanced, the image is passed to the NBIS (NIST Biometric Image Software) toolkit—specifically its MINDTCT (Minutiae Detector) component. This is the same open-source fingerprint analysis library used in law enforcement and government biometrics systems.
MINDTCT scans the ridge map and identifies minutiae points: locations where a ridge line either terminates (a “ridge ending”) or forks into two ridges (a “bifurcation”). For each minutia, it records:
- X/Y coordinates within the image
- Ridge orientation (angle) at that point
- A quality score
A typical fingerprint yields 20–80 minutiae points. These points collectively form a sparse geometric map unique to that finger.
Template Storage
The minutiae map—never the original image—is serialized into a binary template and saved to /var/lib/fprint/<username>/<device>/. The template is owned by root and readable only by fprintd, the fingerprint authentication daemon. Because no photo is stored, there is no way to reconstruct your fingerprint image from the template file alone.
Each enrolled finger gets its own template file. You can inspect enrolled fingers with fprintd-list <username>.
Verification and Matching
At login (or when sudo prompts you), fprintd captures a new scan and runs it through the same enhancement and extraction pipeline to produce a fresh minutiae set. It then performs point-pattern matching against the stored template using a tolerance algorithm that accounts for:
- Translation — your finger will never be placed in exactly the same position
- Rotation — the finger may be tilted slightly each time
- Elastic distortion — skin stretches and compresses differently under pressure
The matcher scores the overlap between the live minutiae and the stored template. If the score exceeds a configurable threshold (set in fprintd’s configuration), authentication succeeds. The entire matching process runs in the fprintd daemon over a D-Bus interface, with PAM (pam_fprintd) acting as the bridge between the system login stack and the daemon.
Security Considerations
Because all processing happens on the host CPU with no hardware-level encryption, this architecture has a wider attack surface than a “Match-on-Chip” sensor. The raw USB image is unencrypted, and a compromised fprintd process could theoretically intercept scans. For a home desktop or personal laptop, the convenience trade-off is generally acceptable—but this is not a suitable solution for high-security environments.
While less secure than hardware-encrypted solutions, this setup provides a significant convenience boost for Linux Mint users on a budget.